
Governments are increasingly attempting to control internet access by blocking websites, filtering protocols, or shutting down networks during political unrest. Countries such as Iran, China, and Russia have built advanced systems to monitor and restrict online communication.
For people living under these restrictions, maintaining access to the open internet often requires circumvention tools such as VPNs, encrypted proxies, and self-hosted tunneling solutions.
One technology that can be used in this situation is Outline, an open-source VPN framework designed to make it easier to deploy private encrypted proxies.
This article explains how Outline works and how it can be used as one option among several tools to bypass network censorship, including in heavily filtered environments.
What is Outline
Outline is an open-source framework developed by Jigsaw (a technology incubator within Alphabet) that allows users to deploy their own encrypted proxy server.
Official site:
https://getoutline.org
Instead of connecting to a commercial VPN provider, Outline lets people or organizations to run their own proxy server on a remote VPS and share access with trusted users.
Outline uses the Shadowsocks protocol, an encrypted proxy designed specifically to help users bypass censorship systems.
Shadowsocks is an open-source encrypted proxy protocol designed to help users bypass internet censorship and network restrictions. It acts as a secure tunnel between your device and a remote server, allowing your internet traffic to pass through networks that might otherwise block certain websites or services.
- It behaves more like encrypted web traffic
- It avoids some easily detectable VPN signatures
- It supports multiple encryption methods
Because of this flexibility, Shadowsocks based tools are often used in environments with heavy filtering.
However, it’s important to understand that no circumvention method is permanently resistant to blocking. Governments frequently adapt their filtering techniques.
Why self-hosted tools matter
Many censorship systems rely on blocking known VPN servers or fingerprinting common VPN protocols.
Most VPN services often suffer from large-scale blocking because thousands of users share the same servers. Once the IP addresses are identified, they are quickly filtered.
Self-hosted solutions change that dynamic.
With tools like Outline:
- The server is deployed privately on a VPS.
- The IP address is not publicly listed.
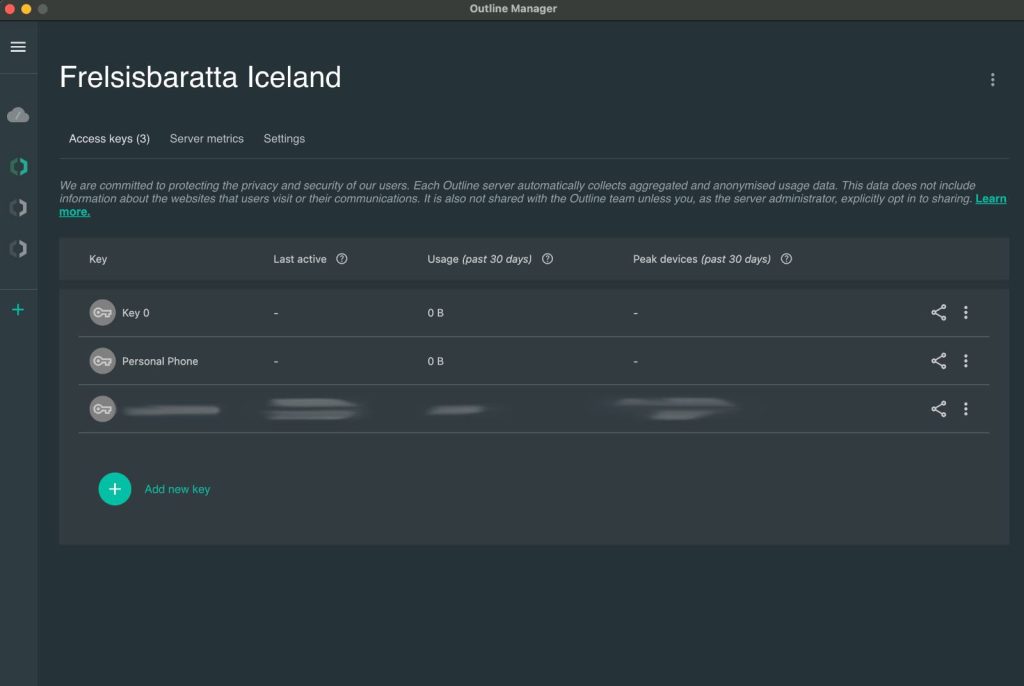
- Access keys can be shared only with trusted users.
This approach makes it harder for automated filtering systems to immediately identify and block connections.
How to set up Outline VPN
Setting up Outline is surprisingly simple.
Step 1
Download the Outline Manager
Official site:
https://getoutline.org
Step 2
Next, you need a VPS server where your proxy will run. Choosing a privacy-focused hosting provider is important because the server will act as your gateway to the open internet. FlokiNET offers hosting infrastructure designed for privacy focused services.
Running your own server on a VPS makes it harder for censorship systems to block access because:
- the IP address is not shared with thousands of VPN users
- the server is privately controlled and can be adapted
Step 3
Deploy the server automatically to your VPS. The software installs the required components and prepares the encrypted proxy environment.
Once the installation finishes, you will receive a connection access key.
Step 4
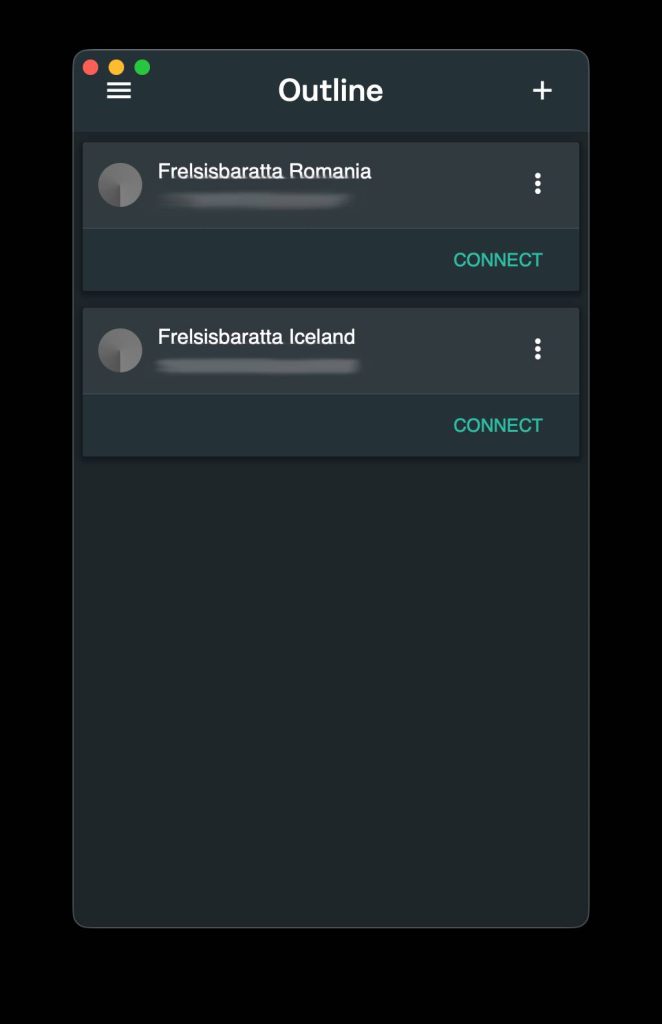
Install the Outline client on your device (Windows, macOS, Android, or iOS) and paste the access key.
Your connection will now route through your private encrypted server.
Limitations:
While Outline can be useful, it is not a universal bypass tool.
In countries like Iran, authorities constantly adapt their filtering systems. For example, some networks have experimented with protocol allow-lists, blocking any traffic that does not match approved protocols.
In practice this means:
- Some Outline servers may be blocked.
- Certain ISPs may detect Shadowsocks traffic.
- IP addresses can eventually be filtered.
Users often need to rotate servers, change ports, or combine multiple technologies.
For this reason, we recommend diversifying circumvention strategies instead of relying on a single tool.
Other anti-censorship tools
Outline is only one piece of a broader ecosystem of circumvention technologies. Other tools commonly used include:
Lantern
https://lantern.io
A peer-to-peer censorship circumvention tool widely used during internet crackdowns in Iran.
Tor (The Onion Router)
https://www.torproject.org
A privacy network that routes traffic through multiple volunteer nodes.
Shadowsocks (standalone servers)
https://shadowsocks.org
The underlying proxy protocol used by Outline.
Satellite distribution systems
Some projects even distribute information through satellite broadcasts to bypass internet restrictions entirely.
Another initiative that supports internet freedom is Snowflake, a Tor network project. Snowflake enables volunteers to run a small proxy server through their browsers to help individuals in censored regions connect to the open internet. If you live in a country with unrestricted internet access, enabling Snowflake is an easy way to help others bypass censorship. By sharing a small amount of your bandwidth, you can help keep information accessible worldwide.
If you want a broader overview of censorship-circumvention techniques, we provides a detailed guide covering multiple tools and strategies. The guide explores several practical approaches including VPNs, Tor, proxies, and other techniques used to maintain access to the open internet.
It Is not bulletproof
Modern censorship systems use technologies such as deep packet inspection (DPI), DNS blocking, and IP filtering to detect and block common VPN traffic. Because of this, relying on a single tool rarely works for long. Users typically combine several approaches such as:
- encrypted proxy protocols like Shadowsocks
- VPNs with obfuscation features
- the Tor network
- DNS-over-HTTPS and encrypted DNS
- SSH tunneling or private proxy servers
Tools like Outline illustrate an important principle: circumvention technology is most resilient when individuals control their own infrastructure rather than relying solely on centralized services.
However, no single solution is permanent. Governments adapt, protocols evolve, and users must remain flexible.
